There is a lot of information about how to verify that an ISO download is both official and contains exactly the data it should. That information is easy to find, served on the same page as the download links themselves, and authenticated by being on an official Fedora https URL.
However, I have tried hard to find the same kind of information for the podman/docker images, and have not been able to find it.
Here is what I was able to find, with a lot of searching:
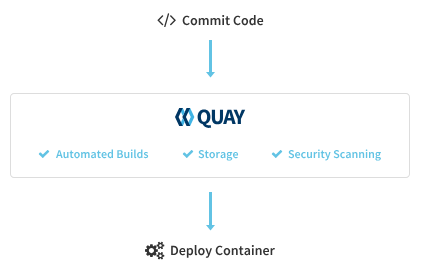
- Various forum posts that strongly imply (but mostly do not directly state) that the “fedora/” namespace on both docker hub and quay.io / registry.fedoraproject.org are the true, official base images… but there is no easy way to fully authenticate these posts.
- Docker images — Fedora Developer Portal - an old page from ~2016 (Fedora 23) that actually clearly states that the Fedora project owns the fedora namespace on Docker.
- Some Fedora subprojects’ documentation pages imply (but again, do not state!) that the “fedora” namespace is the official one - e.g. NeuroFedora has a page titled “Using containers” that shows pulling “fedora:latest” and describes it as “the base Fedora container”.
- There is this page: Verify your Downloaded Image - but it looks infrequently updated. It does link to a recent-looking checksums file that contains sha256 sums for base images with current-looking version numbers; however, these checksums do not match anything in the output of “podman image inspect” or “skopeo image inspect”.
- Various Red Hat pages strongly imply that all images in quay.io are signed, and it looks as if Red Hat may provide a way to confirm the signing key fingerprints, but I’ve found nothing similar for Fedora. And while there are indeed various hashes in the output of “image inspect”, there is nothing that looks like a signing key fingerprint, so nothing to match back to Fedora keeps you safe | The Fedora Project .
I’m 99% certain that the images under the fedora namespace are probably safe, but I’m not able to distinguish between these two cases:
- The images under that namespace are created by the same people responsible for publishing the ISOs, or by a similar team that uses the same level of security.
or
- The container images are a lower-priority project maintained by an unofficial group of volunteers, who don’t have the time/resources to develop a really rigorous set of security practices.
All it would take to satisfy me on this would be one sentence on the “Get Fedora” pages: “We own the ‘fedora’ namespace on Docker Hub and quay.io, and all images published under that namespace are official builds.” Can anyone here both confirm that that’s true, and edit those pages?